Table of Contents
A Computational Framework for Embedding Information into Physical Objects
Summary
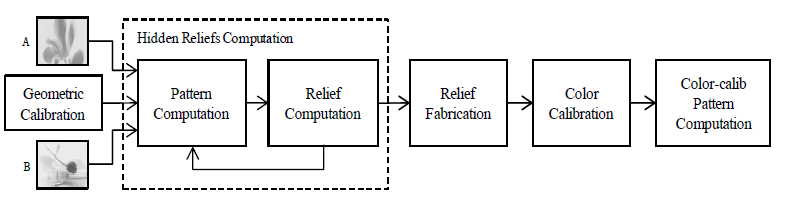
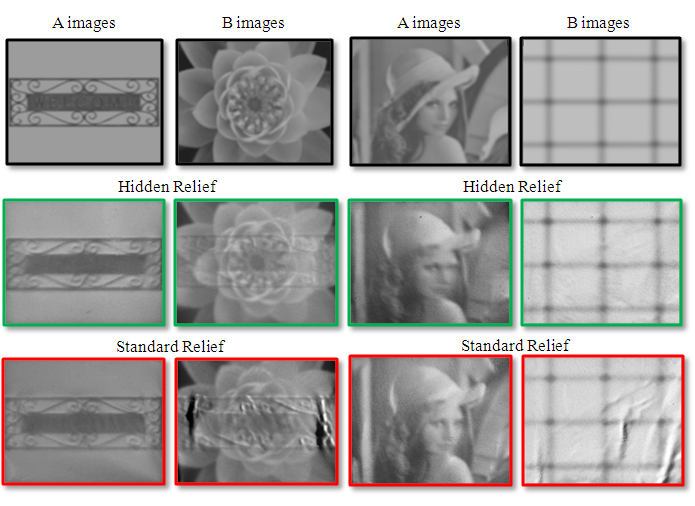
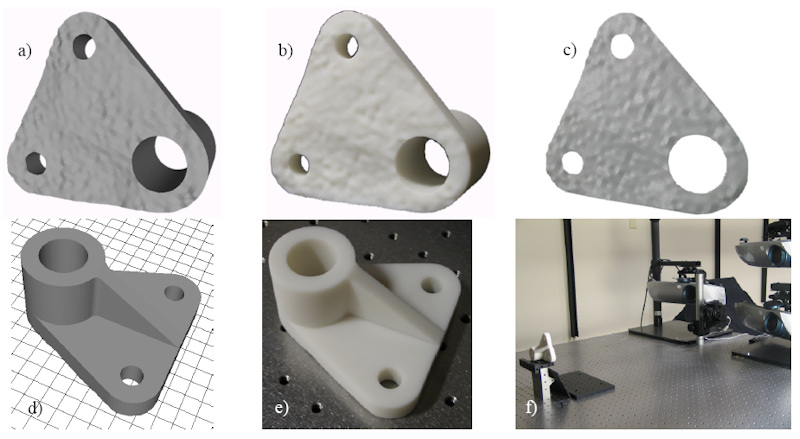
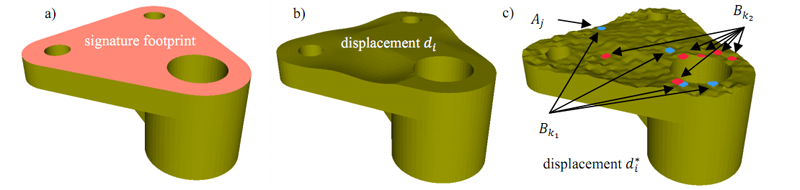
| This NSF-funded project seeks to provide methods to embed into a physical object information for a variety of purposes, including genuinity detection, tamper detection, and multiple appearance generation. Genuinity detection refers to encoding fragile or robust signatures so that a copy, or tampered, version can be differentiated from the original object. Multiple appearance generation refers to generalizing the encoded information from a signature to a different appearance of the same physical object. The project also includes the development of underlying infrastructure for 3D model acquisition and for appearance/signature creation and extraction using projector-based illumination. |
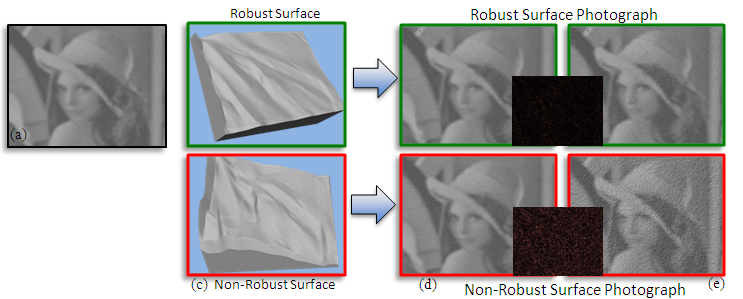
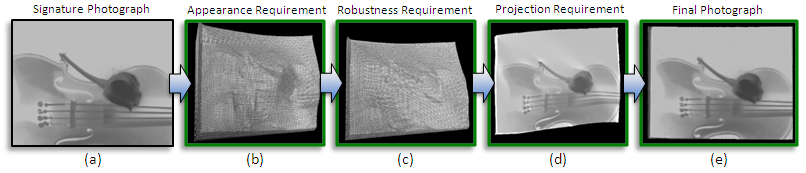
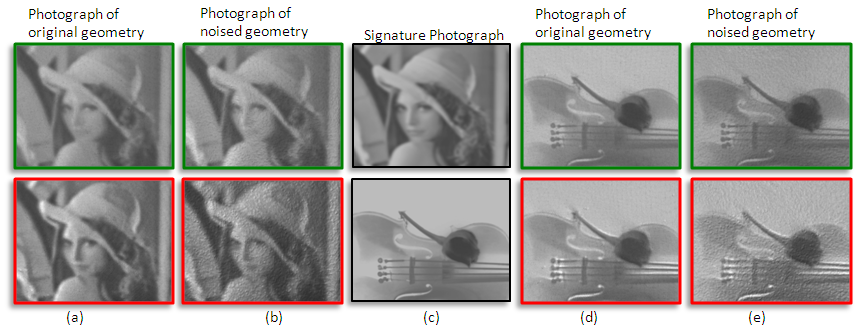
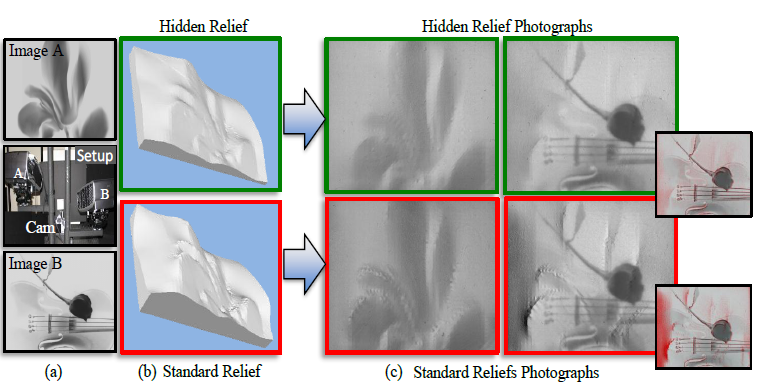
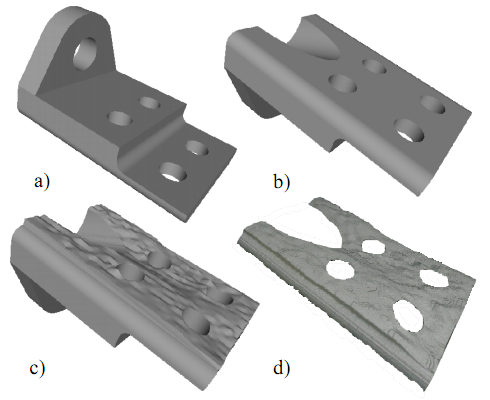
Robustly Embedding Signatures onto Objects
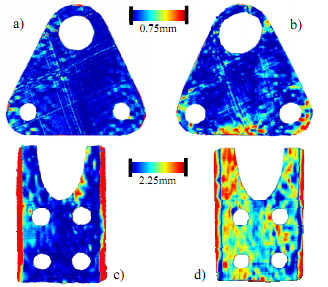
Embedding Spatial Signatures into Printed Documents
| Summary |
|---|
| We have also worked on a 2D version of the problem: the genuinity of printed documents. This should not be thought of as easier than the 3D manufacturing problem, because there are fewer opportunities for embedding genuinity signals, and the available channels turned out to be very noisy (i.e., our own printing of the genuine document can erase the genuinity signal – but we have overcome this difficulty now). We have what looks like a very promising solution (being tested) for the problem of genuinity of printed documents. For the yes/no version of the problem (i.e., genuine printed page or not) we use a technique pioneered by our Purdue ECE colleague Ed Delp and his group to embed a large number of binary 'genuinity votes' in a printed page, a majority of which (around 70%) survive our own printing process. An adversary's scanning of a marked document and re-printing it (possibly after unauthorized alterations) would be detectable because it would entail another round of 30% loss of the binary genuinity votes. We have extended the scheme to go beyond detecting non-genuine printouts, to also pinpoint where in the page unauthorized alterations have been made. Specifically, if the page is a contract or form that can be partitioned into N known sensitive sections (e.g., date, dollar amount, name of beneficiary, signature, terms of delivery, etc) then we can pinpoint which of those were fraudulently modified after scanning the original and re-printing the altered (non-genuine) version. The ongoing experimental evaluation of our scheme is expected to take a few more months of work, and Professor Delp and 2 of his senior PhD students will be co-authors of resulting papers. |
Fragile Signatures for Verifying Object Genuinity
 Research supported in part by NSF CNS Grant No. 0913875 Research supported in part by NSF CNS Grant No. 0913875 |
| Publications |
|---|
|
| People |
|---|
|